共2540部电影 | 今日更新0部
共2540部电影 | 今日更新0部动作片喜剧片爱情片科幻片恐怖片剧情片战争片理论片最新电影 more»
电影《因爱而伟大》
涂松岩,童蕾,孔连顺,黄佳军,韩远琪,郭涛,赵亮,淳于珊珊,晋松,刘亚津
战争片
2022/大陆
更新1080P
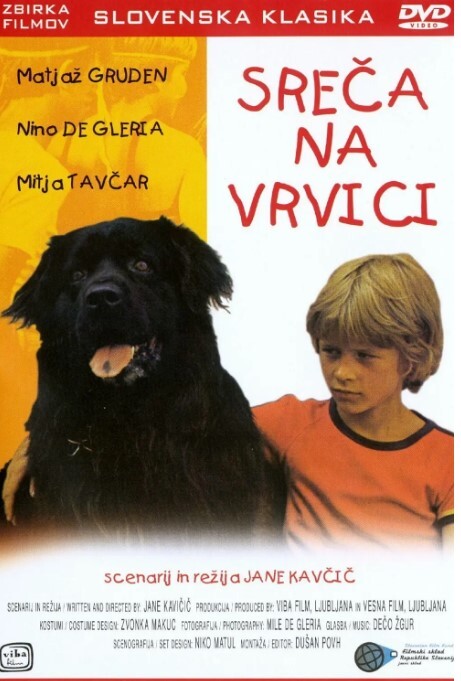
电影《亲亲米莱娜》
Matjaz,Gruden,Matija,Tavcar,Andrej,Djordjevic
喜剧片
1977/南斯拉夫
完美世界在线免费观看
Jason,Chan,Khaleila,Hisham,Simon,Wong
剧情片
2014/新加坡
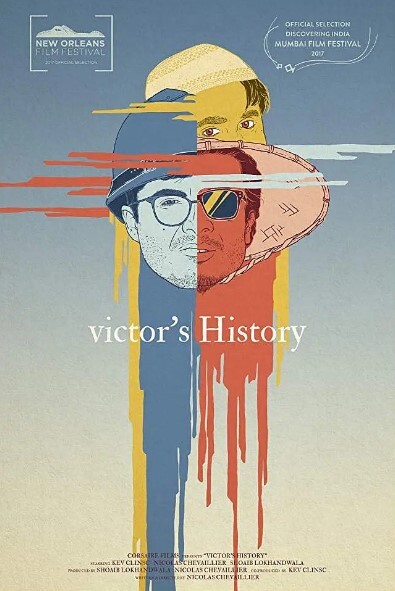
电影维克多的历史
凯夫·克林斯克,尼古拉·舍瓦利埃,绍伊布·洛坎德瓦拉,阿涅斯·布瓦索-海勒,内哈·洛加尼
剧情片
2017/德国,印度
冰海陷落2电影完整版
杰拉德·巴特勒,加里·奥德曼,托比·斯蒂芬斯
动作片
2018/中国大陆,美国,英国
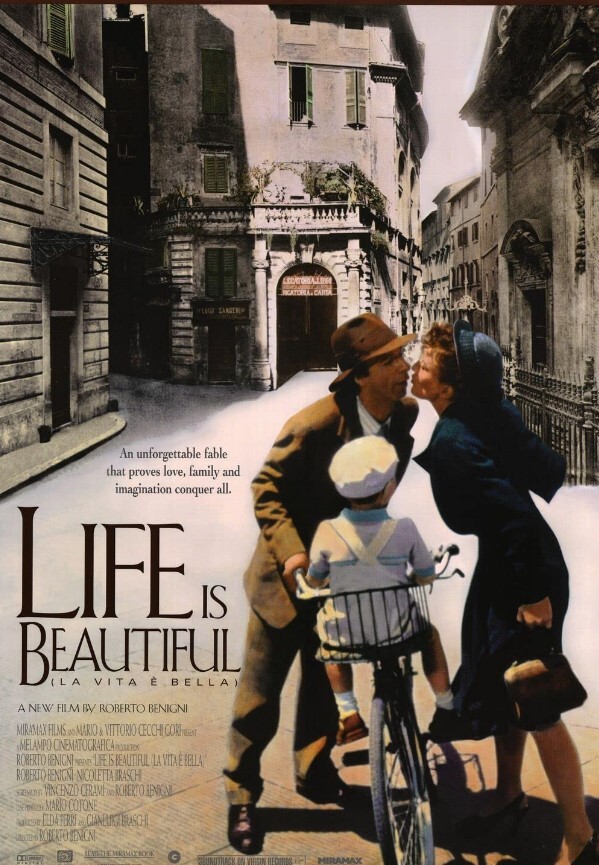
二战电影《美丽人生》免费
罗伯托·贝尼尼,尼可莱塔·布拉斯基,朱斯蒂诺·杜拉诺
剧情片
1997/意大利
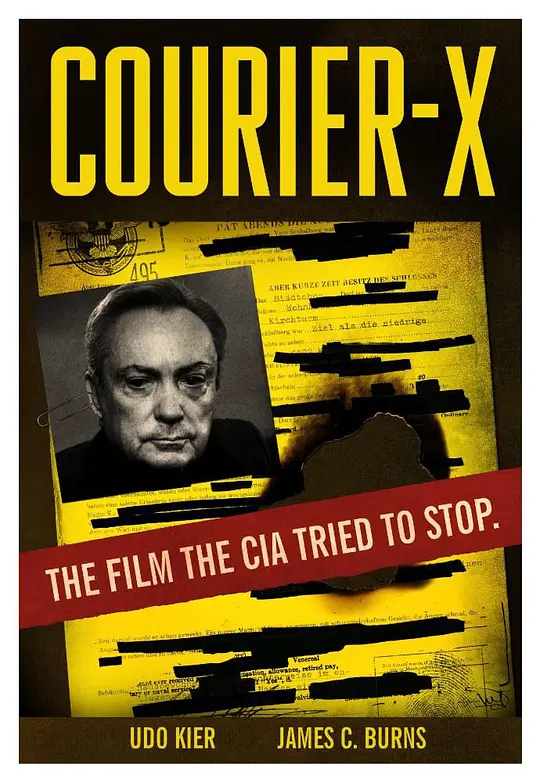
信徒岛未删减版
乌多·基尔,詹姆斯·C·伯恩斯
剧情片
2016/美国
恋之罪完整版电影
李华月,陈伟狄,苏国柱,尹相林,邱惠芳,张国源
爱情片
1995/中国香港
HD中字
霸刀电影完整版
矫明俊,云庄,莫文科,梅吉薇,阮国长
动作片
2023/美国,越南
HD
《李三脚威震地狱门》
闻江龙,游天龙,宋江陵
动作片
1975/中国台湾
HD
电影《灭狼行动》
陈星旭,李瑞超
剧情片
2020/华语
HD
刽子手2015电影
Markiss,McFadden,Paul,Sorvino,Mischa,Barton,
动作片
2017/美国
HD
动作片喜剧片爱情片科幻片恐怖片剧情片战争片理论片
 共63部连续剧 | 今日更新0部
共63部连续剧 | 今日更新0部国产剧日韩剧港台剧欧美剧最新连续剧 more»
小满生活免费在线观看
秦昊,柯蓝,蒋欣,任重,王鸥
国产剧
2023/中国大陆
连载中 连载到32集
《怒海潜沙》在线观看
侯明昊,成毅,李曼,张博宇,刘学义,姚奕辰,姚橹,任嘉伦
国产剧
2019/中国大陆
康熙王朝1-50集免费
斯琴高娃,陈道明,高兰村,茹萍,李建群,朱晏,薛中锐,李楠,安亚平,宫雪花,胡天鸽,李晨涛,刘钧,博弘,廖京生,李洪涛,高田昊,万中良,朱艺丹,姚长安,宋来运,张光正,曹永祥,马小矛,陈斌,苏廷石,刘大印,侯永生,刘毓滨,卢勇,汤加丽,高宏亮,李明,李如平,王也天,陈大中,郝铁男,白杨,崔岱,赵凯,薛亦伦,马捷,李小雷,刘长生,尚言生,关德俊,陈韦辰,刘挺,胡珊珊,赵景文,马子俊
国产剧
2001/中国大陆
完结
国产剧日韩剧港台剧欧美剧
 共5部综艺 | 今日更新0部
共5部综艺 | 今日更新0部